Did you know your TV may be spying on you?
Is your TV spying on YOU? It sounds like science fiction but many new TVs can watch you - telling advertisers your favourite shows or even filming you on the sofa. And there’s no off switch!
You are sitting in bed in your pyjamas, drinking a cup of cocoa. A loved one lies next to you, watching late-night television. Pillow talk is exchanged. An alarm clock is set. Eventually the lights are turned out.
Earlier, you sat on the living-room sofa eating supper, before loading the dishwasher and heading upstairs.
You have, in other words, just enjoyed a perfectly normal night, in a perfectly normal home. The curtains are drawn, the central heating turned up. It’s cosy, relaxing and, above all, completely private. Or so you thought.
The truth turns out to be quite the opposite. For on the other side of the world, people you didn’t know existed are keeping a beady eye on your every move.
These characters can see what clothes you have been wearing and what food you’ve eaten. They heard every word you said, and logged every TV show you watched. Some are criminals, others work for major corporations. And now they know your most intimate secrets.
It may sound like a plot summary for a futuristic science-fiction movie. But real-life versions of this Orwellian scenario are being played out every day in towns and cities across the globe — and in most cases the victims have no idea.
At fault is a common electronic device invented nearly a century ago and found in almost every modern household: the domestic television set.
Put simply, our TVs have started spying on us.
Last week, there was a high-profile case in point. An IT consultant called Jason Huntley, who lives in a village near Hull, uncovered evidence that a flat-screen television, which had been sitting in his living room since the summer, was secretly invading his family’s privacy.
He began investigating the £400 LG device after noticing that its home screen appeared to be showing him ‘targeted’ adverts — for cars, and Knorr stock cubes — based on programmes he’d just been watching.
Huntley decided to monitor information that the so-called smart TV — which connects to the internet — was sending and receiving. He did this by using his laptop effectively as a bridge between his television and the internet receiver, so the laptop was able to show all the data being sucked out of his set.
He soon discovered that details of not just every show he watched but every button he pressed on his remote control were being sent back to LG’s corporate headquarters in South Korea.

There, the electronics company appeared to be using its customers’ data to make money. A promotional video shown to commercial clients suggested that data was being used to provide ‘the ad experience you have always dreamed of’.
The information Huntley’s TV had sent — without his knowledge — included the contents of his private digital video collection, which he’d watched on the television. This included camcorder footage of family celebrations containing images of his wife and two young children.
Most worrying of all, the device continued sending such information to Korea even after Huntley had adjusted the television’s default settings to ‘opt out’ of data sharing.
Huntley wrote about the findings on his blog. After his case was picked up by mainstream news outlets, LG announced an investigation. ‘Customer privacy is a top priority,’ the firm said. ‘We are looking into reports that certain viewing information on LG smart TVs was shared without consent.’
LG has also removed its promotional video about targeted advertising from its website.
The Information Commissioner’s Office says it is now investigating the firm for a ‘possible breach’ of the Data Protection Act. Jason Huntley, meanwhile, tells me he is ‘very suspicious and also a little worried’ by the affair.
‘I don’t think we’ve heard the last of this. Who knows what else these televisions are doing that we don’t know about?’
It doesn’t take much digging to find out. Talk to any IT security expert and they will tell you that Huntley’s discovery is probably the tip of the iceberg.
What’s to blame is the continuing rise of smart televisions, which account for most new TV sets sold and are predicted to be in more than half of British homes by 2016. These high-tech devices differ from traditional televisions in that they are not just passive boxes that receive a signal and transfer it to a backlit screen.
Instead, they are essentially computers that connect to the internet — and so also send information back the other way.
In theory, this can be extremely useful. For example, many smart TVs have shopping ‘apps’ to access Amazon. They connect to iTunes. They allow us to watch YouTube, instantly download films via Netflix, stream BBC shows on iPlayer, and talk to friends using the video phone link Skype.
But in practice, like almost every type of computer, they can be all-too-easily hacked. And unlike PCs, almost all of which have fairly good anti-virus ‘firewalls’, smart TVs have little or no such software. Indeed, most have been designed so that outside software — including anti-virus programmes — can never be installed.
This year, Luigi Auriemma, an IT security researcher and computer programmer from Malta, demonstrated the risks that these devices pose when he showed it was possible to hack into several types of Samsung smart television.
After accessing the devices via the internet, Auriemma was able to control them: turning the TVs off and on, and secretly accessing data they held about a user’s viewing habits.
Had he been a criminal, he could also have obtained details of the credit cards that users had uploaded to access pay-per-view TV, download films or use shopping apps.
Other experts recently made the chilling discovery that it is possible to remotely access the video cameras built into the front of thousands of smart televisions, and spy on the users in their own home.
One such expert is Kurt Stammberger, who works for the IT security firm Mocana. He says the company was recently asked by a television manufacturer to do ‘penetration tests’ on its devices. ‘We weren’t just able to find out what someone was watching, and had watched,’ he says. ‘We could also install “spyware” that could, if they had a video camera, allow us to see through that camera — without even activating the little light that indicates it’s on.
‘It was a fairly straightforward thing to do. People who work in IT often place tape over their computer’s camera lens [in a laptop they are usually set into the inside of the lid] unless they want to actually use it, because it’s so common to hack them. We should all do the same with smart TVs.’
Such an attack, which Stammberger describes as ‘frighteningly easy’ to mount, could provide voyeuristic hackers with a chance to snoop on unsuspecting home-owners in their living rooms or bedrooms.
You have only to witness the extraordinary success of the critically acclaimed Channel 4 show Gogglebox, in which consenting families allow the viewing public to watch them watching television, to appreciate how enticing that prospect could be.
More commercially minded hackers could use such an attack to steal commercial secrets. It could even be used to spy on foreign powers.
‘It’s a serious prospect and I would be very surprised if the Government ever puts in a big order for TVs from, for example, a Chinese manufacturer such as Huawei,’ adds Stammberger, referring to the giant corporation that has been banned in America because of fears over espionage.
‘But supply chains these days are so long and so complex that it’s very rare to buy an electronic device that doesn’t have some sort of Chinese component in it.’
Gangs based largely in Eastern Europe and Russia, meanwhile, are already using so-called ‘data-mining’ programmes to trawl the internet looking for smart TVs in which owners have entered their credit card details. A single search can yield thousands of results.
According to Roger Grimes, who has written eight books on IT security and worked in the field for 28 years, the gangs then sell lists of hacked credit card numbers to fellow criminals.
Card details that were obtained within the past 24 hours sell for around £2.20 each. Older ones are cheaper because there is more chance the cards could have been changed or stopped.
‘What we are starting to see now is really just a foretaste of what’s going to be happening in the next couple of decades,’ says Grimes.
‘Thanks firstly to mobile devices, and now smart TVs, we are entering a brave new world where there will be computers everywhere. Bad guys will take advantage of that.’ And we may not even be safe in our own living rooms.
source: dailymail.co.uk
LG denied any wrong-doing, and issued a statement claiming it would fix any of the privacy issues uncovered by Mr. Huntley.
A shining beacon of hope appears on the horizon:
H.R. 2356:
We Are Watching You Act of 2013
[Congressional Bills 113th Congress] [From the U.S. Government Printing Office] [H.R. 2356 Introduced in House (IH)]So what prompted all of this?113th CONGRESS 1st Session H. R. 2356
To provide for notification to consumers before a video servicecollects visual or auditory information from the viewing area and to provide consumers with choices that do not involve the collection of such information, and for other purposes.
IN THE HOUSE OF REPRESENTATIVES June 13, 2013Mr. Capuano (for himself and Mr. Jones) introduced the following bill; which was referred to the Committee on Energy and Commerce
A BILL To provide for notification to consumers before a video servicecollects visual or auditory information from the viewing area and to provide consumers with choices that do not involve the collection of such information, and for other purposes.
Be it enacted by the Senate and House of Representatives of theUnited States of America in Congress assembled,
SECTION 1. SHORT TITLE.
This Act may be cited as the ``We Are Watching You Act of 2013''.SEC. 2. NOTIFICATION AND CONSUMER CHOICE.
(a) Notification.-- (1) In general.--An operator of a video service may not collect visual or auditory information from the vicinity of the device used to display the video programming stream to the consumer unless the operator-- (A) <strong>displays, as part of the video programming stream, a message that reads, ``<span style="color:#ff0000;">We are watching you.</span>''; and</strong> (B) provides to the consumer a description of the types of information that will be collected and how such information will be used. (2) On-screen message.--The message required by paragraph (1)(A) shall be displayed-- (A) <strong>continuously during the time information is being collected</strong>; and (B) in a color, font, and size that are easily readable at a normal viewing distance. (3) Description of information collected.-- (A) In general.--The description required by paragraph (1)(B) shall be provided as part of the terms and conditions to which the consumer must agree before using the video service. (B) Device provided by operator.--In the case of a video service that is accessed through a device sold or provided to the consumer by the operator of the video service, the description required by paragraph (1)(B) shall be provided as part of the written instructions and other materials accompanying the device, in addition to being provided as required by subparagraph (A). (b) Consumer Choice of Alternative Service.-- (1) In general.--If an operator offers a video service involving the collection of visual or auditory information from the vicinity of the device used to display the video programming stream to the consumer, <strong>such operator shall offer a video service that does not involve the collection of such information but is otherwise identical in all respects</strong>. (2) Device provided by operator.--In the case of a video service that is accessed through a device sold or provided to the consumer by the operator of the video service, the operator shall sell or provide in connection with the alternative service required by paragraph (1) a device that is not capable of collecting such information. (c) Requirements for Information Disclosure.--An operator of avideo service that collects visual or auditory information from the vicinity of the device used to display the video programming stream to the consumer may only disclose such information– (1) with the express consent of the consumer; or (2) as required by a court order issued in connection with a law enforcement investigation. (d) Regulations.–The Commission may promulgate regulations in accordance with section 553 of title 5, United States Code, to implement and enforce this section.
SEC. 3. ENFORCEMENT BY FEDERAL TRADE COMMISSION.
(a) Unfair or Deceptive Acts or Practices.--A violation of section2 or a regulation promulgated under such section shall be treated as a violation of a regulation under section 18(a)(1)(B) of the Federal Trade Commission Act (15 U.S.C. 57a(a)(1)(B)) regarding unfair or deceptive acts or practices. (b) Powers of Commission.–The Commission shall enforce section 2 and the regulations promulgated under such section in the same manner, by the same means, and with the same jurisdiction, powers, and duties as though all applicable terms and provisions of the Federal Trade Commission Act (15 U.S.C. 41 et seq.) were incorporated into and made a part of this Act. Any person who violates such section or a regulation promulgated under such section shall be subject to the penalties and entitled to the privileges and immunities provided in the Federal Trade Commission Act.
SEC. 4. DEFINITIONS.
In this Act: (1) Commission.--The term ``Commission'' means the Federal Trade Commission. (2) Operator.--The term ``operator'' means, with respect to a video service, the person with whom the consumer directly interacts to select and initiate the transmission of the video programming stream. (3) Video service.--The term ``video service'' means the transmission of a video programming stream to consumers by means of the facilities of the operator of the service, the facilities of another person, or any combination thereof. <all></pre>Show your support immediately!
Call your representative, or just click the Call Congress button here.
New Microsoft Patent Uses Kinect And Mobile Cameras To Count People In Your Living Room
A new Microsoft patent will allow the company to remotely surveil, and effectively count American citizens as they order online or cable pay-per-view from the comfort of their own homes.From (CONTENT DISTRIBUTION REGULATION BY VIEWING USER) the patent:
A content presentation system and method allowing content providers to regulate the presentation of content on a per-user-view basis … Consumers are presented with a content selection and a choice of licenses allowing consumption of the content. The users consuming the content on a display device are monitored so that if the number of user-views licensed is exceeded, remedial action may be taken.
The patent, submitted on April 26, 2011, and passed on Nov. 1, 2012, essentially allows the company to remotely turn on any cameras, be they mobile or from something like the XBox Kinect, and count the number of ‘consumers’ watching licensed content.
What Microsoft dubs ‘complex algorithms’ will not only count how many people are consuming that Mixed Martial Arts Championships, but also for how long they consumed the content, paving the way for charging users for half or even quarter uses of content.
From the patent:
In the case of the mobile display device, the display 105 is generally designed for use by one person but it is possible that more than one person may be able to view content on the display 105. As such the consumer detector uses data from the camera or capture device 102 to determine the number of consumers. In one example, camera 102 is an RGB imaging camera and the consumer detector analyzes one or successive images from the camera to ensure that the licensed number of users per view is enforced.
“Enforced” means the patent also gives licensers using Microsoft’s surveillance ‘product’ the right to ‘shut off’ content if an unauthorized amount of users start to watch.
So you may want to tell the folks you invite over for the next fight to shut off their cell phones and remove the batteries prior to beginning the show.
source: www.businessinsider.com

Shaking my head!
Damn the advertisers and their "must know every damn thing about the consumer" attitude, whose greed empowers criminals and the National Security apparatus.Microsoft's Patents for LEGAL INTERCEPT + Content Delivery + Trapwire = 1984
Even without the Big Brother patents and technology, you should still fear the camera:Smile! Hackers Can Silently Access Your Webcam Right Through The Browser (Again)
You know those people who put tape over their laptop's webcam to keep digital peeping toms at bay? They're not crazy.A new proof of concept is making the rounds today that demonstrates how a hacker can snap pics off your webcam, right through the browser, with no consent required.
Well, technically, you are giving consent. You just wouldn’t know it.
Outlined by security consultant Egor Homakov, the hack brings in a few old tricks to work around Flash’s requirement that a user explicitly grants a website permission before it can access their camera or microphone.
Without going into to much detail, the demo uses a bunch of fancy CSS/HTML trickery to render Flash’s permission prompt in a transparent layer, placing the now invisible “Allow” button directly above something the user is likely to click - like, say, the “Play” button on a video.
The basic technique, dubbed Clickjacking, is nothing new. I’d actually generally avoid writing about things like this, if it were new, to keep the word from spreading before the companies got a chance to fix it - but these techniques are already very well known in the hacking world. In fact, a post on Adobe’s security blog suggests that they fixed the bug (or a similar one) way back in 2011. “No user action or Flash Player product update are required,” it reads.
And yet… it still works. We tested the proof of concept on the latest build of Chrome for Mac, and it pulled from our webcam without issue or any visible prompt. Others have found the exploit to work on IE10, but it seems to be patched on the most recent releases of Safari and Firefox. When it works, the only evidence that the camera was ever accessed is a near instant and oh-so-easy-to-miss blink of the LED indicator.
[UPDATE: Google has acknowledged and fixed the bug in Chrome with version 27.0.1453.116, released six days after our initial report on 6/13]
You can test the [WARNING] proof of concept yourself here (Heads Up: If you consider girls in bikinis to be NSFW, that link is NSFW. Also, it’ll take a picture of you, though the author claims he’s not storing them - but clarifies that someone could, if they wanted).
If your browser doesn’t visibly render the permission box and clicking the play button snaps a picture of you, your browser fails the test. If it shows the permission box or blocks the click, you’re safe (from this specific exploit, at least).
So, why is this a big deal? Imagine you’re perusing some of the Internet’s more, erm, intimatewebsites. You’ve fallen down the rabbit hole, finding yourself 3 or 4 sites away from the trusted one you started at. You click “Play” on something that suits your particular fancy and.. surprise! The LED on your webcam flicks on, and two seconds later you’re looking at a freshly snapped picture of yourself on screen, hands …wherever they might be.
Fortunately, getting a solid layer of protection against such exploits moving forward is pretty straightforward. For one, you can tape up that webcam - it’s a bit tinfoil hat, sure, but it’s better than having a photo of your bad bits blasted out to the Internet on some shady-ass Tumblr. Second, consider using Firefox* with something like NoScript, disabling it only for trusted sites.
Oh, and yeah, insert the obligatory NSA/PRISM joke here.
[*NoScript-esque extensions exist for Chrome, but I’ve yet to find one that is as dependable or user-friendly] source: techcrunch.com
CONCLUSION:
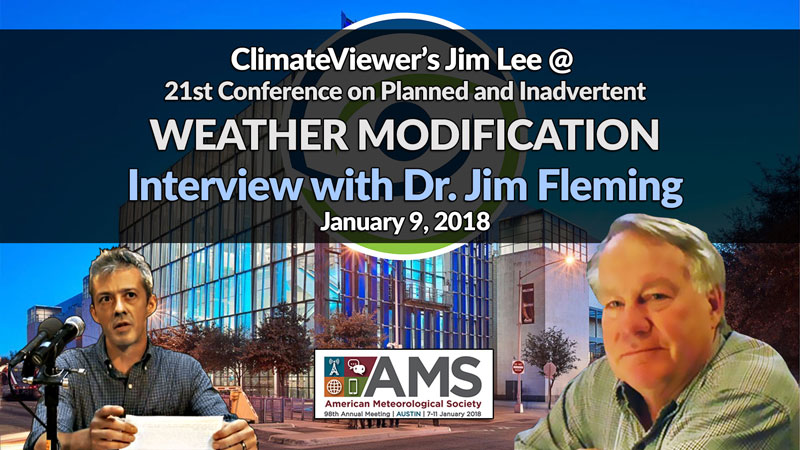
ClimateViewer Says: